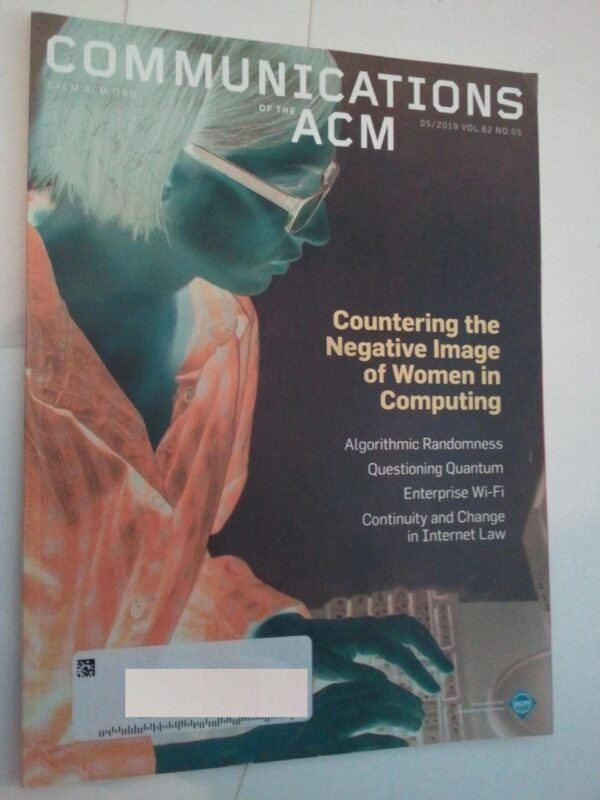
Communication of the ACM Magazine 5/2019 Vol 62 # 5 Negative Image of Women in Computing
$39.99
Description
Communication of the ACM Magazine 5/2019 Vol 62 # 5 Negative Image of Women in Computing
Communications of the ACM is the monthly journal of the Association for Computing Machinery. It was established in 1958, with Saul Rosen as its first managing editor. It is sent to all ACM members. Articles are intended for readers with backgrounds in all areas of computer science and information systems.
EDITORIAL
Quantum hype and quantum skepticism
OPINION
Don’t ignore the cost of ’embedded energy’
RESEARCH-ARTICLE
Implementing guidelines for governance, oversight of AI, and automation
RESEARCH-ARTICLE
Questioning quantum
Researchers hunt for ways to keep quantum computing honest.
RESEARCH-ARTICLE
Code talkers
Using voice input to write programs.
RESEARCH-ARTICLE
Deep insecurities: the internet of things shifts technology risk
A more connected world sounds alluring, but without better protections, the Internet of Things could lead to disaster.
COLUMN: Law and technology
OPINION
Continuity and change in internet law
The fundamentals of the field of Internet law have remained consistent, but details have evolved in response to technological innovation.
COLUMN: Privacy and security
OPINION
Encryption and surveillance
Why the law-enforcement access question will not just go away.
OPINION
What does it mean for a computing curriculum to succeed?
Examining the expansion, proliferation, and integration of computing education everywhere.
OPINION
Enterprise wi-fi: we need devices that are secure by default
Seeking to increase awareness of WPA2 Enterprise network security technology flaws and reduce risk to users.
RESEARCH-ARTICLE
Achieving digital permanence
The many challenges to maintaining stored information and ways to overcome them.
RESEARCH-ARTICLE
Online event processing
Achieving consistency where distributed transactions have failed.
RESEARCH-ARTICLE
Net neutrality: unexpected solution to blockchain scaling
Cloud-delivery networks could dramatically improve blockchains’ scalability, but clouds must be provably neutral first.
RESEARCH-ARTICLE
Countering the negative image of women in computing
A positive image would inspire the capable but underrepresented who might otherwise give up on computing.
RESEARCH-ARTICLE
The limit of blockchains: infeasibility of a smart Obama-Trump contract
Although smart contracts are Turing complete, it is a misconception that they can fulfill all routine contracts.
REVIEW-ARTICLE
Algorithmic randomness
Tracing some of the latest advancements in algorithmic randomness.
SECTION: Research highlights
OTHER
Technical perspective: Compressing matrices for large-scale machine learning
RESEARCH-ARTICLE
Compressed linear algebra for declarative large-scale machine learning
Large-scale Machine Learning (ML) algorithms are often iterative, using repeated read-only data access and I/O-bound matrix-vector multiplications. Hence, it is crucial for performance to fit the data into single-node or distributed main memory to …
RESEARCH-ARTICLE
Like old times
From the intersection of computational science and technological speculation, with boundaries limited only by our ability to imagine what could be.
The Furby singularity promises eternal conversation with the untimely departed.
Subjects
Security and privacy
Linear algebra algorithms
Machine learning
Quantum computing
API languages
Artificial intelligence
Codes of ethics
Computing / technology policy
Computing standards, RFCs and guidelines
Digital libraries and archives
E-commerce infrastructure
Education
Electronic commerce
Event-driven architectures
Human computer interaction (HCI)
Information storage technologies
IT governance
Law, social and behavioral sciences
Models of computation
Network algorithms
Network security
Network services
Quantum computation
Quantum error correction and fault tolerance
Quantum technologies
Random order and robust communication complexity
Randomness, geometry and discrete structures
Robotics
Security in hardware
Software and application security
Software and its engineering
Software development methods
Software development techniques
Surveillance
Wireless access points, base stations and infrastructure
Address label on cover. Minor wear to cover. Otherwise in unread condition. More pictures may be in description (which it is suggested you read!)
Related products
-
Comics Buyer’s Guide 1679 Jul 2011 Green Lantern’s Evolution Cvr DC Animated P D
$29.99 Add to cart -

Game Informer 189 NM Uncharted 2 Cvr Dead Space Metallica Left 4 Dead
$29.99 Add to cart -

Game Informer 199 NM Disney’s Epic Mickey Cvr Dragon Age Diablo 3 Left 4 Dead 2
$29.99 Add to cart -

Game Informer 306 Call of Duty Black Ops 4 Fallout Cyberpunk 2077 World Warcraft
$29.99 Add to cart